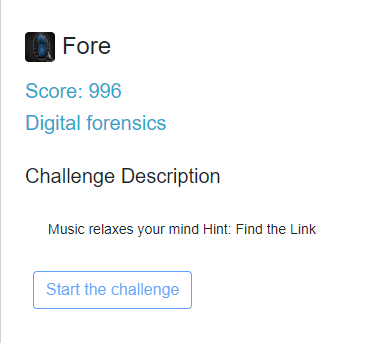
Razi CTF - Writeup
FORE
So loading up the pcap with Wireshark and applying the filter "http.content_type matches "audio/*" gave the following result
Following the TCP stream, gives us the link !!
http://www.coca.ir/ey-iran-gholamhossein-banan-music/
The flag for this is RaziCTF{http://www.coca.ir/ey-iran-gholamhossein-banan-music/}
CYBERCRIME
Tricky , but simple .. google search reveals the following link
https://twitter.com/kvbNDtxL0kmIqRU/status/1052074801433595904
The flag for this CTF is RaziCTF{@kvbNDtxL0kmIqRU}
CLICHE
File provided by the challenge was a .wav file. It wasn't comprehensible. After running tools like exiftool and binwalk, I knew for sure that the flag wasn't hidden in the file itself.
Finally I decided to check the .wav file with qsstv software. This is what I got:





For the cliche challenge, what is qsstv? And how did you know it was going to work? Like, was it a random guess?
ReplyDeleteHi Sta, I knew what qsstv is. As I had faced a smiliar ctf challenge just like this before.
Deletehey Sta
ReplyDeleteyou can checkout this article for qsstv explanation
https://ourcodeworld.com/articles/read/956/how-to-convert-decode-a-slow-scan-television-transmissions-sstv-audio-file-to-images-using-qsstv-in-ubuntu-18-04